Software Supply chain attack Playbook
If short on time directly jump to the playbooks section.
Here we talk about how a Supply chain attack can be mitigated in general. A specific use case will be the SolarWinds supply chain attack – Link and the log4j vulnerabilities – Link
- It is important for an organization to have a list of all the software the company uses, their licenses and versions
- Know what are the most important business applications and what they are composed of.
- Software – Bill of Materials (SBOM) is the first step in handling supply chain attacks. Broadly referred C-SCRM
- Understand how software is built in today’s world. The actual code developed by the company could be a few hundreds or thousands of lines of code. But the third-party libraries/code used could run 1000X more.
Key reference documents
- Clear detailed overview from CISA – https://www.cisa.gov/sites/default/files/publications/defending_against_software_supply_chain_attacks_508.pdf
- Basics from Blackhat talk – http://i.blackhat.com/USA-19/Thursday/us-19-Doerr-The-Enemy-Within-Modern-Supply-Chain-Attacks.pdf
Please note that unintended software is like malware or malicious code. Hence most containment and mitigations could be around the same workflows as Malware/Malicious code.
Playbook
FlexibleIR provides you with different flavors of best practice playbooks for the same threat.
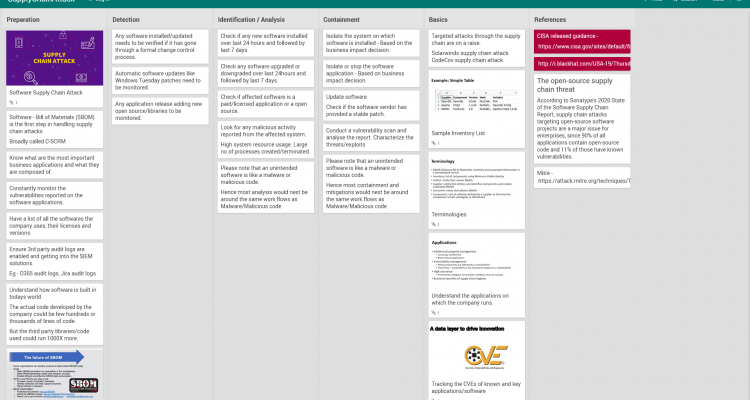
Mitigations
Broad level mitigations could be:
- Isolate the system on which software is installed – Based on the business impact decision.
- Isolate or stop the software application – Based on business impact decision.
- Update software – Check if the software vendor has provided a stable patch.
- Please note that an unintended software is like a malware or malicious code. Hence most containment and mitigations could next be around the same work flows as Malware/Malicious code.
Analysis
Identification & Scoping of the incident is key. Please refer to the playbooks above.
Threat hunting
Threat hunters need to build quick hypotheses and run the threat hunting activities. They need to be enabled with human-centered simplified tools to quickly get to the action.
Tips
Know whom to call. Please first ensure you are able to quickly mobilize all the help required and the right contacts have been reached out to. You may need to start on several parallel investigation trails. General actions to Recover If Impacted– Don’t Let a Bad Day Get Worse.
- Ask for help! Contact CISA, the FBI, or the Secret Service (If in US) . Respective CERTs for every country.
- Work with an experienced advisor to help recover from a cyber attack
- Isolate the infected systems and phase your return to operations
- Review the connections of any business relationships (customers, partners, vendors) that touch your network
- Apply business impact assessment findings to prioritize recovery
- Fact – how the attackers got access – will likely take time to determine. So have parallel tracks running for immediate containment and investigative/forensic works.
References
Innovations
Thinking out of the box is key when a major breach has happened and everything is down. Here is an example of creative thinking down at HYDRO during their incident remediation phase.
Automation
Consider possible automation candidate scripts to reduce impact time.
User Contributed Notes
FlexibleIR aims to provide state-of-the-art playbooks by utilizing the power of the community to build on quality playbooks. Readers add their operation knowledge and thoughts to make every playbook evolving and better.
Revisions
May 10, 2021: Initial Version