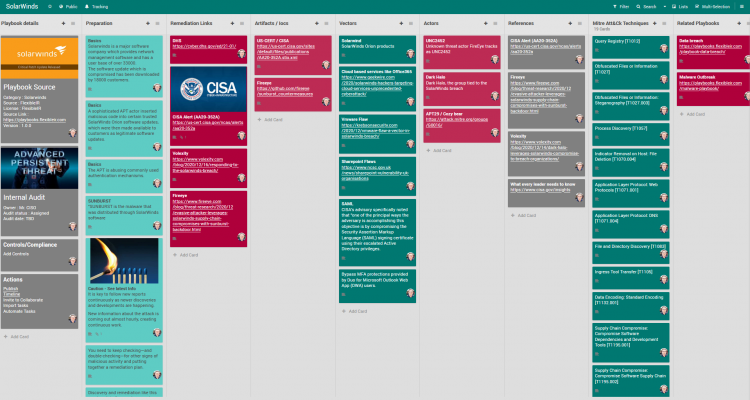
SolarWinds Sunburst Incident Response Playbook
If short on time directly jump to the playbooks section.
It is key to follow new reports continuously as newer discoveries and developments are happening. Ensure to see article time stamps.
- https://us-cert.cisa.gov/ncas/alerts/aa20-352a
- https://www.fireeye.com/blog/threat-research/2020/12/evasive-attacker-leverages-solarwinds-supply-chain-compromises-with-sunburst-backdoor.html
- https://github.com/fireeye/sunburst_countermeasures
- Volexity blog – Link
The SolarWinds supply chain attacks are sophisticated in execution, broad in scope, and incredibly potent in their effectiveness. “SUNBURST is the malware that was distributed through SolarWinds software
An advanced persistent threat (APT) actor is responsible for compromising the SolarWinds Orion software supply chain, as well as widespread abuse of commonly used authentication mechanisms. This threat actor has the resources, patience, and expertise to gain access to and privileges over highly sensitive information if left unchecked.
You need to keep checking—and double-checking—for other signs of malicious activity and putting together a remediation plan. Discovery and remediation like this require a lot of manual processing. Searching for indicator lists, gathering threat intelligence, and building out a playbook all take time and resources, which are in short supply during a potential breach. Plus, new information about the attack is coming out almost hourly, creating continuous work.
Playbook
FlexibleIR provides you different flavors of best practice playbooks for the same threat.
Mitigations
For SolarWinds Orion Owners
Owners of vulnerable SolarWinds Orion products will generally fall into one of three categories.
- Category 1 (updated December 19, 2020) includes those who do not have the identified malicious binary. These owners (except federal agencies subject to ED 21-01) can patch their systems and resume use as determined by and consistent with their internal risk evaluations.
- Category 2 includes those who have identified the presence of the malicious binary—with or without beaconing to
avsvmcloud[.]com. Owners with malicious binary whose vulnerable appliances only unexplained external communications are withavsvmcloud[.]com—a fact that can be verified by comprehensive network monitoring for the device—can harden the device, re-install the updated software from a verified software supply chain, and resume use as determined by and consistent with a thorough risk evaluation. - Category 3 includes those with the binary beaconing to
avsvmcloud[.]comand secondary C2 activity to a separate domain or IP address. If you observed communications withavsvmcloud[.]comthat appear to suddenly cease prior to December 14, 2020— not due to an action taken by your network defenders—you fall into this category. Assume the environment has been compromised, and initiate incident response procedures immediately.
Breach Response Templates
Refer – https://playbooks.flexibleir.com/cyber-incident-breach-communication-or-disclosure-templates/
Analysis
Identification & Scoping of incident is key. Please refer the playbooks above.
Tips
Know whom to call. Please first ensure you are able to quickly mobilize all the help required and the right contacts have been reached out to. You may need to start on several parallel investigation trails. General actions to Recover If Impacted– Don’t Let a Bad Day Get Worse.
- Ask for help! Contact CISA, the FBI, or the Secret Service (If in US) . Respective CERTs for every country.
- Work with an experienced advisor to help recover from a cyber attack
- Isolate the infected systems and phase your return to operations
- Review the connections of any business relationships (customers, partners, vendors) that touch your network
- Apply business impact assessment findings to prioritize recovery
- Fact – how the attackers got access – will likely take time to determine. So have parallel tracks running for immediate containment and investigative/forensic works.
References
References
Innovations
Thinking out of the box is key when a major breach has happened and everything is down. Here is an example of creative thinking down at HYDRO during their incident remediation phase.
Automation
Consider possible automation candidate scripts to reduce impact time.
User Contributed Notes
FlexibleIR aims to provide state-of-the-art playbooks by utilizing the power of the community to build on quality playbooks. Readers add their operation knowledge and thoughts to make every playbook evolving and better.
Revisions
March 13, 2020: Initial Version