May 8, 2020
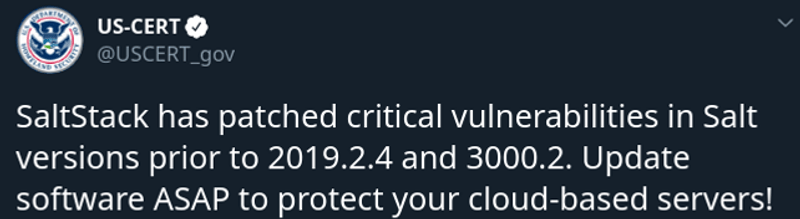
Playbook for attack on Salt servers
Nov3, 2020 – New vulnerabilities revealed. The fixed versions include 3002.1, 3001.3, and 3000.5 depending on what branch of Salt you are using. The company has also made patches available for older versions, such as 2019.x. https://www.bleepingcomputer.com/news/security/saltstack-reveals-new-critical-vulnerabilities-patch-now/ Older vulnerabilities – The hackers use CVE-2020-11651 (an authentication bypass) and CVE-2020-11652 (a directory traversal) to take control over Salt master server Mitigations Below are for older bug fixes related […]