Log4j CVE-2021-44228 Incident response Playbook
If short on time directly jump to the playbooks section.
It is key to follow new reports continuously as newer discoveries and developments are happening. Ensure to see article time stamps.
- Quick SANS video – https://www.youtube.com/watch?v=oC2PZB5D3Ys
Playbook
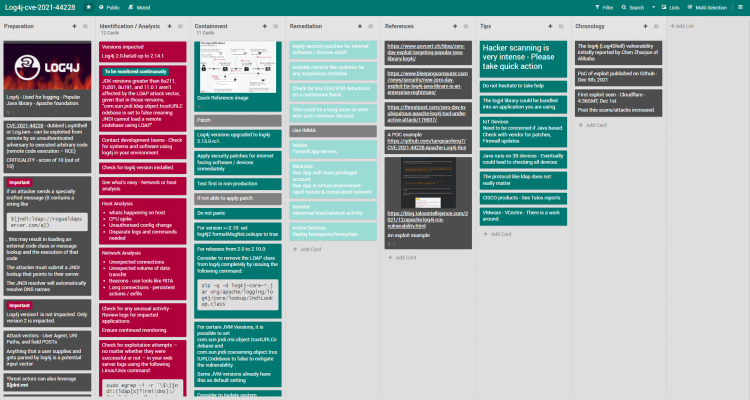
Mitigations
Apply Patch
Log4j versions upgraded to log4j-2.15.0-rc1. Test first on non-production systems.
In case not able to apply the patch
- For version >=2.10: set log4j2.formatMsgNoLookups to true.
- For releases from 2.0 to 2.10.0:
- Consider to remove the LDAP class from log4j completely by issuing the following command:
- zip -q -d log4j-core-*.jar org/apache/logging/log4j/core/lookup/JndiLookup.class
- For certain JVM Versions, it is possible to set com.sun.jndi.rmi.object.trustURLCodebase and com.sun.jndi.cosnaming.object.trustURLCodebase to false to mitigate the vulnerability.
- Some JVM versions already have this as default setting
Breach/Attack Response Communication Templates
Refer – https://playbooks.flexibleir.com/cyber-incident-breach-communication-or-disclosure-templates/
Analysis
Identification & Scoping of the incident is key. Please refer to the playbooks above.
Tips
Know whom to call. Please first ensure you are able to quickly mobilize all the help required and the right contacts have been reached out to. You may need to start on several parallel investigation trails. General actions to Recover If Impacted– Don’t Let a Bad Day Get Worse.
Innovations
Thinking out of the box is key when a major attack/breach has happened and everything is down. Here is an example of creative thinking down at HYDRO during their incident remediation phase.
Automation
Consider possible automation candidate scripts to reduce impact time.
User Contributed Notes
FlexibleIR aims to provide state-of-the-art playbooks by utilizing the power of the community to build on quality playbooks. Readers add their operation knowledge and thoughts to make every playbook evolving and better.
Revisions
Dec 13, 2021: Initial Version