- Nov3, 2020 – New vulnerabilities revealed. The fixed versions include 3002.1, 3001.3, and 3000.5 depending on what branch of Salt you are using. The company has also made patches available for older versions, such as 2019.x.
- Older vulnerabilities – The hackers use CVE-2020-11651 (an authentication bypass) and CVE-2020-11652 (a directory traversal) to take control over Salt master server
Mitigations
Below are for older bug fixes related to CVE-2020-11651
- Consider taking down the related servers to investigate the incident and patch vulnerable servers.
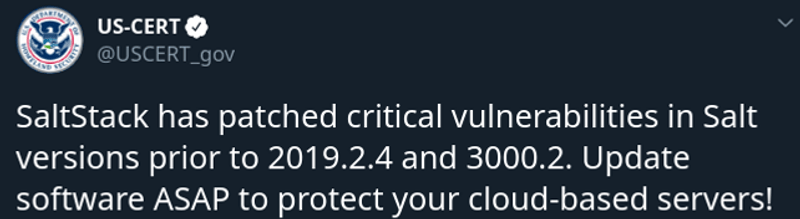
- Patches for the Salt vulnerabilities have been released earlier this week. Salt servers should normally be deployed behind a firewall and not left exposed on the internet.
- SaltStack engineers patched these vulnerabilities in release 3000.2 and users of Salt are encouraged to make sure that their installs are configured to automatically pull updates from SaltStacks repository server, see https://repo.saltstack.com/ for more information. A patch release for the previous major release version is also available, with version number 2019.2.4.
- Adding network security controls that restrict access to the salt master (ports 4505 and 4506 being the defaults) to known minions, or at least block the wider Internet, would also be prudent as the authentication and authorization controls provided by Salt are not currently robust enough to be exposed to hostile networks.
- Have a quick look at related incidents [1][2][3][4]
Technical Details
Understanding your adversary is half battle won. Details at : https://labs.f-secure.com/advisories/saltstack-authorization-bypass
Analysis
- Abnormal CPU utilization or servers going down.
- The hackers could have installed a backdoor and a cryptocurrency miner on your server.
References
Technical details
https://labs.f-secure.com/advisories/saltstack-authorization-bypass
https://nvd.nist.gov/vuln/detail/CVE-2020-11651
https://nvd.nist.gov/vuln/detail/CVE-2020-11652
https://www.cvedetails.com/vulnerability-list/vendor_id-12943/product_id-26420/Saltstack-Salt.html
Related Incidents
https://www.zdnet.com/article/cisco-discloses-security-breach-that-impacted-virl-pe-infrastructure/
https://www.zdnet.com/article/search-provider-algolia-discloses-security-incident-due-to-salt-vulnerability/
https://www.zdnet.com/article/hackers-breach-lineageos-servers-via-unpatched-vulnerability/
https://www.zdnet.com/article/ghost-blogging-platform-servers-hacked-and-infected-with-crypto-miner/
https://www.computerweekly.com/news/252482595/Xen-Orchestra-latest-victim-of-Salt-cryptojackers
More references in news
https://www.tenable.com/blog/cve-2020-11651-cve-2020-11652-critical-salt-framework-vulnerabilities-exploited-in-the-wild
https://www.csoonline.com/article/3541721/cloud-servers-hacked-via-critical-saltstack-vulnerabilities.html
Post navigation
Venkat is founder of FlexibleIR. He brings 20 years of experience in building tools and products at Sun Microsystems, Intel, Novell, HP, Yahoo,Tesco and startups. He has developed test suites and frameworks for post silicon validation of the Xeon processor family (Fuzzing). He has worked deeply on UFS files system at SUN Microsystem. Was a security paranoid at Yahoo.