Online education platform threats and mitigations
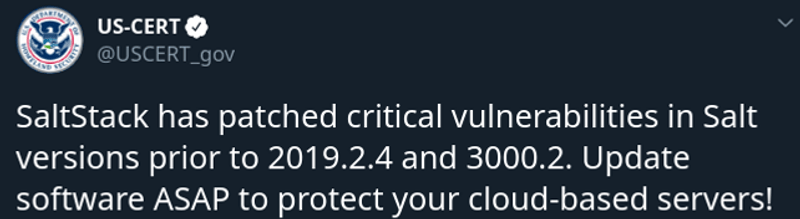
The rapid shift to online learning brought about by the pandemic is all but guaranteed to increase the threats they are facing and incidents they will experience. Typical users of online learning platforms – students, lecturers or teachers. Typical types Online training with content. Online training by trainers Large educational institutes – Going online. A platform for educators and learners with educators creating educational videos […]